Common misconceptions about IPv6 security | APNIC Blog
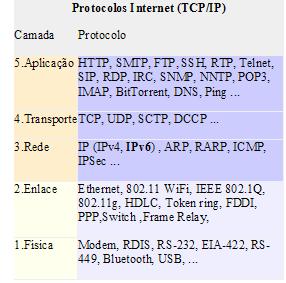
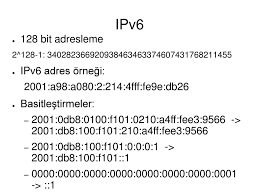
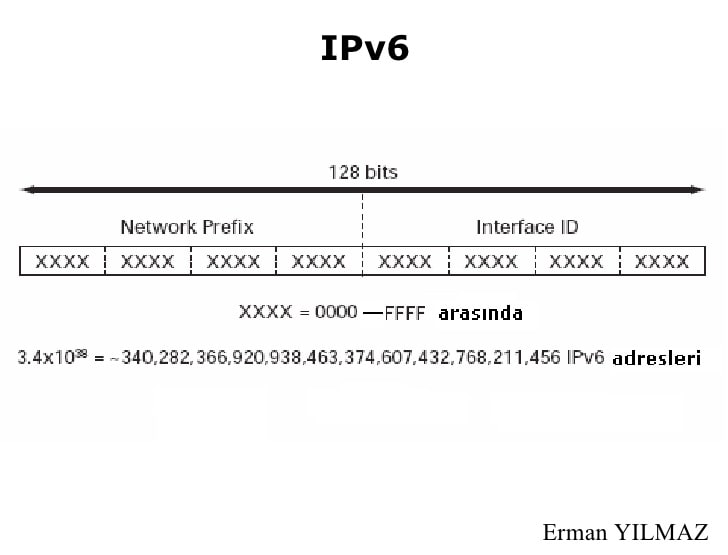
Misconceptions can be dangerous. This is especially true when they lead to network this post I’ll seek to set the record straight for several of the most common misconceptions about IPv6 security. IPv6 is more/less secure than IPv4There are two big misconceptions about IPv6 security:IPv6 is more secure than IPv4IPv6 is less secure than IPv4Neither are true. Both assume that comparing IPv6 security with IPv4 security is meaningful. It is ’s networks, whether they have IPv6 deployed in them or not, are largely IPv6 compatible. All modern operating systems and network devices employ IPv6 dual-stacks, in which IPv6 is turned on by default. Even if you have not actively deployed IPv6, your networks still have the combined vulnerability surface of IPv4 and erefore, comparing IPv4 security with IPv6 security is meaningless. They both have the vulnerabilities of IPv4 and IPv6. Every network should be secured for IPv4 and IPv6. Ideally, you should have done this well over a decade ago. IPv6 is IPv4 with longer addressesIn network security, it is crucial not to underestimate the scale of risks. The most common misconception that I have heard in my twenty years of working with IPv6 is that IPv6 is IPv4 with longer addresses. It is not. IPv6 is vastly different from IPv4, often in complex and subtle ways. Sometimes, what is best practice in IPv4 is the opposite of best practice in IPv6 misconceptions: It’s fake newsIt is not possible to list all the differences here. Instead, I will illustrate this using addressing. This is one area where superficially the difference between IPv4 and IPv6 appears obvious. However, not only are IPv6 addresses longer, they are also inherently different in attributes, types, structure and how they are used. For example:They have new attributes: length, scope and is normal for IPv6 interfaces to have multiple addresses. IPv6 addresses can change over lticast plays a crucial role in core IPv6 are a vast number of methods for assigning interface identifiers (the bottom 64 bits) IPv6 addresses are used and managed is hugely public addresses are is only addressing. IPv6 has many other differences both in things we are familiar with in IPv4 and in completely new protocols and features. All of these have security implications; the biggest being that staff will not appreciate the differences, and therefore the need, to secure give you a feel for the scope of the IPv6 vulnerability surface, I have included the figure below. Of course, it is not intended to compare IPv4 and IPv6 security (indeed IPv4 is included). However, it does illustrate that there are many new areas to consider, some of which are significant. Figure 1 — The IPv6 vulnerability makes IPv6 more secure than IPv4Internet Protocol Security (IPsec) was designed to provide network layer security (authentication and encryption). It was included as a mandatory feature in the IPv6 standards. Many believed, and some still believe, that this gives IPv6 an advantage over are two reasons why this is not the case. Firstly, while including IPsec functionality in the IPv6 stack was mandatory, using IPsec is not mandatory. Secondly, IPv4 also has IPsec, so there is no difference. Or is there? IPsec in IPv4 is often used for VPNs. These are terminated at the edge of networks. IPv4 IPsec is rarely used to secure end-to-end traffic. This is because of the widespread use of Network Address Translation in IPv4 (NAT44). NAT44 mangles the IPv4 headers and breaks IPsec. In IPv6 this restriction does not exist. Using IPsec end-to-end becomes more practical. IPv6 is already facilitating new and innovative ways of using IPsec. We have clients who are using IPv6 IPsec to secure all traffic within their data centres. We also have clients who have deployed IPv6 to leverage IPsec based end-to-end security allowing them to decommission their existing VPN dress scanning is impossible in IPv6The enormous number of IPv6 subnet addresses (264 = 18, 446, 744, 073, 709, 551, 616) is often thought to make it impossible for attackers to scan IPv6 subnets. There is some truth in this. To sequentially scan a gigabit ethernet subnet would take 491, 351 years if there is no other ever, it is not impossible for an attacker to find addresses in a subnet, it is simply harder. How hard depends on the type of addresses that you are using and where the scanner is Zesplot: visualizing IPv6 address spaceIf the network’s IPv6 addresses have a known structure, then scanning them becomes much easier. For example, some organizations number their hosts sequentially: for example, 1, 2, 3. This is the first sequence a scanner is likely to base their IPv6 address structure on IPv4 addresses. This is not considered to be a good idea. From a security perspective, it makes address scanning as trivial as it is in an IPv4 network. Even networks that use modified EUI-64 addresses that are based on MAC addresses can be scanned if an attacker has enough prior, the use of opaque static and privacy addresses can make remote IPv6 address scanning impractical. However, discovering addresses by other means may still be timating the time required to scan an IPv6 subnet: Length of Neighbour Solicitation frame (including the preamble and interframe gap) = 840 bitsTime to send Neighbour Solicitation on gigabit ethernet = 0. 00000084 secondsTime to transmit all 264 Neighbour Solicitation = 1. 54953 x 1013 seconds= 1. 54953 x 1013/31536000 = 491351. 6306 years(Assumes that there is no other traffic on the subnet! )No NAT makes IPv6 insecureOne of the most common misconceptions regarding IPv6 security is that the lack of NAT makes IPv6 less secure. NAT44 is often seen as a security feature in IPv4 networks. The use of public addresses in IPv6 and the restoration of end-to-end connectivity is of great concern to many IPv4 network nfusing brokenness with security is a mistake. Firewalls can easily provide equivalent and better protection than NAT without breaking end-to-end connectivity. Ironically, NAT44 and its associated myriad of NAT-traversal techniques have many security issues of their lessonsThese are just a few of the most common misconceptions about IPv6 security. There are many key lessons are:Don’t underestimate the scale of the differences between IPv6 and IPv4 networks need to be secured against IPv6 network and security staff need to be competent in IPv6 and in IPv6 security IPv6 is deployed will influence how secure it is in a longer introduction to IPv6 security threats and security features, watch my presentation at the UK IPv6 Council on IPv6 Security David Holder is CEO and chief consultant at Erion Ltd. He has over twenty years’ experience providing IPv6 consultancy and training to enterprises and organizations around the views expressed by the authors of this blog are their own
and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
IPsec – Wikipedia
In computing, Internet Protocol Security (IPsec) is a secure network protocol suite that authenticates and encrypts the packets of data to provide secure encrypted communication between two computers over an Internet Protocol network. It is used in virtual private networks (VPNs).
IPsec includes protocols for establishing mutual authentication between agents at the beginning of a session and negotiation of cryptographic keys to use during the session. IPsec can protect data flows between a pair of hosts (host-to-host), between a pair of security gateways (network-to-network), or between a security gateway and a host (network-to-host). [1]
IPsec uses cryptographic security services to protect communications over Internet Protocol (IP) networks. It supports network-level peer authentication, data origin authentication, data integrity, data confidentiality (encryption), and replay protection.
The initial IPv4 suite was developed with few security provisions. As a part of the IPv4 enhancement, IPsec is a layer 3 OSI model or internet layer end-to-end security scheme. In contrast, while some other Internet security systems in widespread use operate above layer 3, such as Transport Layer Security (TLS) that operates above the Transport Layer and Secure Shell (SSH) that operates at the Application layer, IPsec can automatically secure applications at the IP layer.
History[edit]
Starting in the early 1970s, the Advanced Research Projects Agency sponsored a series of experimental ARPANET encryption devices, at first for native ARPANET packet encryption and subsequently for TCP/IP packet encryption; some of these were certified and fielded. From 1986 to 1991, the NSA sponsored the development of security protocols for the Internet under its Secure Data Network Systems (SDNS) program. [2] This brought together various vendors including Motorola who produced a network encryption device in 1988. The work was openly published from about 1988 by NIST and, of these, Security Protocol at Layer 3 (SP3) would eventually morph into the ISO standard Network Layer Security Protocol (NLSP). [3]
From 1992 to 1995, various groups conducted research into IP-layer encryption.
1. In 1992, the US Naval Research Laboratory (NRL) began the Simple Internet Protocol Plus (SIPP) project to research and implement IP encryption.
2. In 1993, at Columbia University and AT&T Bell Labs, John Ioannidis and others researched the software experimental Software IP Encryption Protocol (swIPe) on SunOS.
3. In 1993, Sponsored by Whitehouse internet service project, Wei Xu at Trusted Information Systems (TIS) further researched the Software IP Security Protocols and developed the hardware support for the triple DES Data Encryption Standard, [4] which was coded in the BSD 4. 1 kernel and supported both x86 and SUNOS architectures. By December 1994, TIS released their DARPA-sponsored open-source Gauntlet Firewall product with the integrated 3DES hardware encryption at over T1 speeds. It was the first-time using IPSec VPN connections between the east and west coast of the States, known as the first commercial IPSec VPN product.
4. Under NRL’s DARPA-funded research effort, NRL developed the IETF standards-track specifications (RFC 1825 through RFC 1827) for IPsec, which was coded in the BSD 4. 4 kernel and supported both x86 and SPARC CPU architectures. [5] NRL’s IPsec implementation was described in their paper in the 1996 USENIX Conference Proceedings. [6] NRL’s open-source IPsec implementation was made available online by MIT and became the basis for most initial commercial implementations. [5]
The Internet Engineering Task Force (IETF) formed the IP Security Working Group in 1992[7] to standardize openly specified security extensions to IP, called IPsec. [8] In 1995, the working group organized a few of the workshops with members from the five companies (TIS, CISCO, FTP, Checkpoint, etc. ). During the IPSec workshops, the NRL’s standards and Cisco and TIS’ software are standardized as the public references, published as RFC-1825 through RFC-1827. [9]
Security architecture[edit]
The IPsec is an open standard as a part of the IPv4 suite. IPsec uses the following protocols to perform various functions:[10][11]
Authentication Headers (AH) provides connectionless data integrity and data origin authentication for IP datagrams and provides protection against replay attacks. [12][13]
Encapsulating Security Payloads (ESP) provides confidentiality, connectionless data integrity, data origin authentication, an anti-replay service (a form of partial sequence integrity), and limited traffic-flow confidentiality. [1]
Internet Security Association and Key Management Protocol (ISAKMP) provides a framework for authentication and key exchange, [14] with actual authenticated keying material provided either by manual configuration with pre-shared keys, Internet Key Exchange (IKE and IKEv2), Kerberized Internet Negotiation of Keys (KINK), or IPSECKEY DNS records. [15][16][17][18] The purpose is to generate the Security Associations (SA) with the bundle of algorithms and parameters necessary for AH and/or ESP operations.
[edit]
Usage of IPsec Authentication Header format in Tunnel and Transport modes
The Security Authentication Header (AH) was developed at the US Naval Research Laboratory in the early 1990s and is derived in part from previous IETF standards’ work for authentication of the Simple Network Management Protocol (SNMP) version 2. Authentication Header (AH) is a member of the IPsec protocol suite. AH ensures connectionless integrity by using a hash function and a secret shared key in the AH algorithm. AH also guarantees the data origin by authenticating IP packets. Optionally a sequence number can protect the IPsec packet’s contents against replay attacks, [19] using the sliding window technique and discarding old packets.
In IPv4, AH prevents option-insertion attacks. In IPv6, AH protects both against header insertion attacks and option insertion attacks.
In IPv4, the AH protects the IP payload and all header fields of an IP datagram except for mutable fields (i. e. those that might be altered in transit), and also IP options such as the IP Security Option (RFC 1108). Mutable (and therefore unauthenticated) IPv4 header fields are DSCP/ToS, ECN, Flags, Fragment Offset, TTL and Header Checksum. [13]
In IPv6, the AH protects most of the IPv6 base header, AH itself, non-mutable extension headers after the AH, and the IP payload. Protection for the IPv6 header excludes the mutable fields: DSCP, ECN, Flow Label, and Hop Limit. [13]
AH operates directly on top of IP, using IP protocol number 51. [20]
The following AH packet diagram shows how an AH packet is constructed and interpreted:[12][13]
Authentication Header format
Offsets
Octet16
0
1
2
3
Bit10
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
Next Header
Payload Len
Reserved
32
Security Parameters Index (SPI)
64
Sequence Number
C
96
Integrity Check Value (ICV)………
Next Header (8 bits)
Type of the next header, indicating what upper-layer protocol was protected. The value is taken from the list of IP protocol numbers.
Payload Len (8 bits)
The length of this Authentication Header in 4-octet units, minus 2. For example, an AH value of 4 equals 3×(32-bit fixed-length AH fields) + 3×(32-bit ICV fields) − 2 and thus an AH value of 4 means 24 octets. Although the size is measured in 4-octet units, the length of this header needs to be a multiple of 8 octets if carried in an IPv6 packet. This restriction does not apply to an Authentication Header carried in an IPv4 packet.
Reserved (16 bits)
Reserved for future use (all zeroes until then).
Security Parameters Index (32 bits)
Arbitrary value which is used (together with the destination IP address) to identify the security association of the receiving party.
Sequence Number (32 bits)
A monotonic strictly increasing sequence number (incremented by 1 for every packet sent) to prevent replay attacks. When replay detection is enabled, sequence numbers are never reused, because a new security association must be renegotiated before an attempt to increment the sequence number beyond its maximum value. [13]
Integrity Check Value (multiple of 32 bits)
Variable length check value. It may contain padding to align the field to an 8-octet boundary for IPv6, or a 4-octet boundary for IPv4.
Encapsulating Security Payload[edit]
Usage of IPsec Encapsulating Security Payload (ESP) in Tunnel and Transport modes
The IP Encapsulating Security Payload (ESP)[21] was developed at the Naval Research Laboratory starting in 1992 as part of a DARPA-sponsored research project, and was openly published by IETF SIPP[22] Working Group drafted in December 1993 as a security extension for SIPP. This ESP was originally derived from the US Department of Defense SP3D protocol, rather than being derived from the ISO Network-Layer Security Protocol (NLSP). The SP3D protocol specification was published by NIST in the late 1980s, but designed by the Secure Data Network System project of the US Department of Defense.
Encapsulating Security Payload (ESP) is a member of the IPsec protocol suite. It provides origin authenticity through source authentication, data integrity through hash functions and confidentiality through encryption protection for IP packets. ESP also supports encryption-only and authentication-only configurations, but using encryption without authentication is strongly discouraged because it is insecure. [23][24][25]
Unlike Authentication Header (AH), ESP in transport mode does not provide integrity and authentication for the entire IP packet. However, in Tunnel Mode, where the entire original IP packet is encapsulated with a new packet header added, ESP protection is afforded to the whole inner IP packet (including the inner header) while the outer header (including any outer IPv4 options or IPv6 extension headers) remains unprotected. ESP operates directly on top of IP, using IP protocol number 50. [20]
The following ESP packet diagram shows how an ESP packet is constructed and interpreted:[1][26]
Encapsulating Security Payload format
Payload data………………
Padding (0-255 octets)……
Pad Length
Next Header……
Arbitrary value used (together with the destination IP address) to identify the security association of the receiving party.
A monotonically increasing sequence number (incremented by 1 for every packet sent) to protect against replay attacks. There is a separate counter kept for every security association.
Payload data (variable)
The protected contents of the original IP packet, including any data used to protect the contents (e. g. an Initialisation Vector for the cryptographic algorithm). The type of content that was protected is indicated by the Next Header field.
Padding (0-255 octets)
Padding for encryption, to extend the payload data to a size that fits the encryption’s cipher block size, and to align the next field.
Pad Length (8 bits)
Size of the padding (in octets).
Type of the next header. The value is taken from the list of IP protocol numbers.
Security association[edit]
The IPsec protocols use a security association, where the communicating parties establish shared security attributes such as algorithms and keys. As such IPsec provides a range of options once it has been determined whether AH or ESP is used. Before exchanging data the two hosts agree on which algorithm is used to encrypt the IP packet, for example DES or IDEA, and which hash function is used to ensure the integrity of the data, such as MD5 or SHA. These parameters are agreed for the particular session, for which a lifetime must be agreed and a session key. [27]
The algorithm for authentication is also agreed before the data transfer takes place and IPsec supports a range of methods. Authentication is possible through pre-shared key, where a symmetric key is already in the possession of both hosts, and the hosts send each other hashes of the shared key to prove that they are in possession of the same key. IPsec also supports public key encryption, where each host has a public and a private key, they exchange their public keys and each host sends the other a nonce encrypted with the other host’s public key. Alternatively if both hosts hold a public key certificate from a certificate authority, this can be used for IPsec authentication. [28]
The security associations of IPsec are established using the Internet Security Association and Key Management Protocol (ISAKMP). ISAKMP is implemented by manual configuration with pre-shared secrets, Internet Key Exchange (IKE and IKEv2), Kerberized Internet Negotiation of Keys (KINK), and the use of IPSECKEY DNS records. [18][29][30] RFC 5386 defines Better-Than-Nothing Security (BTNS) as an unauthenticated mode of IPsec using an extended IKE protocol. C. Meadows, C. Cremers, and others have used Formal Methods to identify various anomalies which exist in IKEv1 and also in IKEv2. [31]
In order to decide what protection is to be provided for an outgoing packet, IPsec uses the Security Parameter Index (SPI), an index to the security association database (SADB), along with the destination address in a packet header, which together uniquely identifies a security association for that packet. A similar procedure is performed for an incoming packet, where IPsec gathers decryption and verification keys from the security association database.
For IP multicast a security association is provided for the group, and is duplicated across all authorized receivers of the group. There may be more than one security association for a group, using different SPIs, thereby allowing multiple levels and sets of security within a group. Indeed, each sender can have multiple security associations, allowing authentication, since a receiver can only know that someone knowing the keys sent the data. Note that the relevant standard does not describe how the association is chosen and duplicated across the group; it is assumed that a responsible party will have made the choice.
Modes of operation[edit]
The IPsec protocols AH and ESP can be implemented in a host-to-host transport mode, as well as in a network tunneling mode.
Transport mode[edit]
In transport mode, only the payload of the IP packet is usually encrypted or authenticated. The routing is intact, since the IP header is neither modified nor encrypted; however, when the authentication header is used, the IP addresses cannot be modified by network address translation, as this always invalidates the hash value. The transport and application layers are always secured by a hash, so they cannot be modified in any way, for example by translating the port numbers.
A means to encapsulate IPsec messages for NAT traversal has been defined by RFC documents describing the NAT-T mechanism.
Tunnel mode[edit]
In tunnel mode, the entire IP packet is encrypted and authenticated. It is then encapsulated into a new IP packet with a new IP header. Tunnel mode is used to create virtual private networks for network-to-network communications (e. between routers to link sites), host-to-network communications (e. remote user access) and host-to-host communications (e. private chat). [32]
Tunnel mode supports NAT traversal.
Algorithms[edit]
Symmetric encryption algorithms[edit]
Cryptographic algorithms defined for use with IPsec include:
HMAC-SHA1/SHA2 for integrity protection and authenticity.
TripleDES-CBC for confidentiality
AES-CBC and AES-CTR for confidentiality.
AES-GCM and ChaCha20-Poly1305 providing confidentiality and authentication together efficiently.
Refer to RFC 8221 for details.
Key exchange algorithms[edit]
Diffie–Hellman (RFC 3526)
ECDH (RFC 4753)
Authentication algorithms[edit]
RSA
ECDSA (RFC 4754)
PSK (RFC 6617)
Implementations[edit]
The IPsec can be implemented in the IP stack of an operating system, which requires modification of the source code. This method of implementation is done for hosts and security gateways. Various IPsec capable IP stacks are available from companies, such as HP or IBM. [33] An alternative is so called bump-in-the-stack (BITS) implementation, where the operating system source code does not have to be modified. Here IPsec is installed between the IP stack and the network drivers. This way operating systems can be retrofitted with IPsec. This method of implementation is also used for both hosts and gateways. However, when retrofitting IPsec the encapsulation of IP packets may cause problems for the automatic path MTU discovery, where the maximum transmission unit (MTU) size on the network path between two IP hosts is established. If a host or gateway has a separate cryptoprocessor, which is common in the military and can also be found in commercial systems, a so-called bump-in-the-wire (BITW) implementation of IPsec is possible. [34]
When IPsec is implemented in the kernel, the key management and ISAKMP/IKE negotiation is carried out from user space. The NRL-developed and openly specified “PF_KEY Key Management API, Version 2” is often used to enable the application-space key management application to update the IPsec Security Associations stored within the kernel-space IPsec implementation. [35] Existing IPsec implementations usually include ESP, AH, and IKE version 2. Existing IPsec implementations on UNIX-like operating systems, for example, Solaris or Linux, usually include PF_KEY version 2.
Embedded IPsec can be used to ensure the secure communication among applications running over constrained resource systems with a small overhead. [36]
Standards status[edit]
IPsec was developed in conjunction with IPv6 and was originally required to be supported by all standards-compliant implementations of IPv6 before RFC 6434 made it only a recommendation. [37] IPsec is also optional for IPv4 implementations. IPsec is most commonly used to secure IPv4 traffic. [citation needed]
IPsec protocols were originally defined in RFC 1825 through RFC 1829, which were published in 1995. In 1998, these documents were superseded by RFC 2401 and RFC 2412 with a few incompatible engineering details, although they were conceptually identical. In addition, a mutual authentication and key exchange protocol Internet Key Exchange (IKE) was defined to create and manage security associations. In December 2005, new standards were defined in RFC 4301 and RFC 4309 which are largely a superset of the previous editions with a second version of the Internet Key Exchange standard IKEv2. These third-generation documents standardized the abbreviation of IPsec to uppercase “IP” and lowercase “sec”. “ESP” generally refers to RFC 4303, which is the most recent version of the specification.
Since mid-2008, an IPsec Maintenance and Extensions (ipsecme) working group is active at the IETF. [38][39]
Alleged NSA interference[edit]
In 2013, as part of Snowden leaks, it was revealed that the US National Security Agency had been actively working to “Insert vulnerabilities into commercial encryption systems, IT systems, networks, and endpoint communications devices used by targets” as part of the Bullrun program. [40] There are allegations that IPsec was a targeted encryption system. [41]
The OpenBSD IPsec stack came later on and also was widely copied. In a letter which OpenBSD lead developer Theo de Raadt received on 11 Dec 2010 from Gregory Perry, it is alleged that Jason Wright and others, working for the FBI, inserted “a number of backdoors and side channel key leaking mechanisms” into the OpenBSD crypto code. In the forwarded email from 2010, Theo de Raadt did not at first express an official position on the validity of the claims, apart from the implicit endorsement from forwarding the email. [42] Jason Wright’s response to the allegations: “Every urban legend is made more real by the inclusion of real names, dates, and times. Gregory Perry’s email falls into this category. … I will state clearly that I did not add backdoors to the OpenBSD operating system or the OpenBSD crypto framework (OCF). “[43] Some days later, de Raadt commented that “I believe that NETSEC was probably contracted to write backdoors as alleged. … If those were written, I don’t believe they made it into our tree. “[44] This was published before the Snowden leaks.
An alternative explanation put forward by the authors of the Logjam attack suggests that the NSA compromised IPsec VPNs by undermining the Diffie-Hellman algorithm used in the key exchange. In their paper[45] they allege the NSA specially built a computing cluster to precompute multiplicative subgroups for specific primes and generators, such as for the second Oakley group defined in RFC 2409. As of May 2015, 90% of addressable IPsec VPNs supported the second Oakley group as part of IKE. If an organization were to precompute this group, they could derive the keys being exchanged and decrypt traffic without inserting any software backdoors.
A second alternative explanation that was put forward was that the Equation Group used zero-day exploits against several manufacturers’ VPN equipment which were validated by Kaspersky Lab as being tied to the Equation Group[46] and validated by those manufacturers as being real exploits, some of which were zero-day exploits at the time of their exposure. [47][48][49] The Cisco PIX and ASA firewalls had vulnerabilities that were used for wiretapping by the NSA[citation needed].
Furthermore, IPsec VPNs using “Aggressive Mode” settings send a hash of the PSK in the clear. This can be and apparently is targeted by the NSA using offline dictionary attacks. [50][51][52]
IETF documentation[edit]
Standards track[edit]
RFC 1829: The ESP DES-CBC Transform
RFC 2403: The Use of HMAC-MD5-96 within ESP and AH
RFC 2404: The Use of HMAC-SHA-1-96 within ESP and AH
RFC 2405: The ESP DES-CBC Cipher Algorithm With Explicit IV
RFC 2410: The NULL Encryption Algorithm and Its Use With IPsec
RFC 2451: The ESP CBC-Mode Cipher Algorithms
RFC 2857: The Use of HMAC-RIPEMD-160-96 within ESP and AH
RFC 3526: More Modular Exponential (MODP) Diffie-Hellman groups for Internet Key Exchange (IKE)
RFC 3602: The AES-CBC Cipher Algorithm and Its Use with IPsec
RFC 3686: Using Advanced Encryption Standard (AES) Counter Mode With IPsec Encapsulating Security Payload (ESP)
RFC 3947: Negotiation of NAT-Traversal in the IKE
RFC 3948: UDP Encapsulation of IPsec ESP Packets
RFC 4106: The Use of Galois/Counter Mode (GCM) in IPsec Encapsulating Security Payload (ESP)
RFC 4301: Security Architecture for the Internet Protocol
RFC 4302: IP Authentication Header
RFC 4303: IP Encapsulating Security Payload
RFC 4304: Extended Sequence Number (ESN) Addendum to IPsec Domain of Interpretation (DOI) for Internet Security Association and Key Management Protocol (ISAKMP)
RFC 4307: Cryptographic Algorithms for Use in the Internet Key Exchange Version 2 (IKEv2)
RFC 4308: Cryptographic Suites for IPsec
RFC 4309: Using Advanced Encryption Standard (AES) CCM Mode with IPsec Encapsulating Security Payload (ESP)
RFC 4543: The Use of Galois Message Authentication Code (GMAC) in IPsec ESP and AH
RFC 4555: IKEv2 Mobility and Multihoming Protocol (MOBIKE)
RFC 4806: Online Certificate Status Protocol (OCSP) Extensions to IKEv2
RFC 4868: Using HMAC-SHA-256, HMAC-SHA-384, and HMAC-SHA-512 with IPsec
RFC 4945: The Internet IP Security PKI Profile of IKEv1/ISAKMP, IKEv2, and PKIX
RFC 5280: Internet X. 509 Public Key Infrastructure Certificate and Certificate Revocation List (CRL) Profile
RFC 5282: Using Authenticated Encryption Algorithms with the Encrypted Payload of the Internet Key Exchange version 2 (IKEv2) Protocol
RFC 5386: Better-Than-Nothing Security: An Unauthenticated Mode of IPsec
RFC 5529: Modes of Operation for Camellia for Use with IPsec
RFC 5685: Redirect Mechanism for the Internet Key Exchange Protocol Version 2 (IKEv2)
RFC 5723: Internet Key Exchange Protocol Version 2 (IKEv2) Session Resumption
RFC 5857: IKEv2 Extensions to Support Robust Header Compression over IPsec
RFC 5858: IPsec Extensions to Support Robust Header Compression over IPsec
RFC 7296: Internet Key Exchange Protocol Version 2 (IKEv2)
RFC 7321: Cryptographic Algorithm Implementation Requirements and Usage Guidance for Encapsulating Security Payload (ESP) and Authentication Header (AH)
RFC 7383: Internet Key Exchange Protocol Version 2 (IKEv2) Message Fragmentation
RFC 7427: Signature Authentication in the Internet Key Exchange Version 2 (IKEv2)
RFC 7634: ChaCha20, Poly1305, and Their Use in the Internet Key Exchange Protocol (IKE) and IPsec
Experimental RFCs[edit]
RFC 4478: Repeated Authentication in Internet Key Exchange (IKEv2) Protocol
Informational RFCs[edit]
RFC 2367: PF_KEY Interface
RFC 2412: The OAKLEY Key Determination Protocol
RFC 3706: A Traffic-Based Method of Detecting Dead Internet Key Exchange (IKE) Peers
RFC 3715: IPsec-Network Address Translation (NAT) Compatibility Requirements
RFC 4621: Design of the IKEv2 Mobility and Multihoming (MOBIKE) Protocol
RFC 4809: Requirements for an IPsec Certificate Management Profile
RFC 5387: Problem and Applicability Statement for Better-Than-Nothing Security (BTNS)
RFC 5856: Integration of Robust Header Compression over IPsec Security Associations
RFC 5930: Using Advanced Encryption Standard Counter Mode (AES-CTR) with the Internet Key Exchange version 02 (IKEv2) Protocol
RFC 6027: IPsec Cluster Problem Statement
RFC 6071: IPsec and IKE Document Roadmap
RFC 6379: Suite B Cryptographic Suites for IPsec
RFC 6380: Suite B Profile for Internet Protocol Security (IPsec)
RFC 6467: Secure Password Framework for Internet Key Exchange Version 2 (IKEv2)
Best current practice RFCs[edit]
RFC 5406: Guidelines for Specifying the Use of IPsec Version 2
Obsolete/historic RFCs[edit]
RFC 1825: Security Architecture for the Internet Protocol (obsoleted by RFC 2401)
RFC 1826: IP Authentication Header (obsoleted by RFC 2402)
RFC 1827: IP Encapsulating Security Payload (ESP) (obsoleted by RFC 2406)
RFC 1828: IP Authentication using Keyed MD5 (historic)
RFC 2401: Security Architecture for the Internet Protocol (IPsec overview) (obsoleted by RFC 4301)
RFC 2406: IP Encapsulating Security Payload (ESP) (obsoleted by RFC 4303 and RFC 4305)
RFC 2407: The Internet IP Security Domain of Interpretation for ISAKMP (obsoleted by RFC 4306)
RFC 2409: The Internet Key Exchange (obsoleted by RFC 4306)
RFC 4305: Cryptographic Algorithm Implementation Requirements for Encapsulating Security Payload (ESP) and Authentication Header (AH) (obsoleted by RFC 4835)
RFC 4306: Internet Key Exchange (IKEv2) Protocol (obsoleted by RFC 5996)
RFC 4718: IKEv2 Clarifications and Implementation Guidelines (obsoleted by RFC 7296)
RFC 4835: Cryptographic Algorithm Implementation Requirements for Encapsulating Security Payload (ESP) and Authentication Header (AH) (obsoleted by RFC 7321)
RFC 5996: Internet Key Exchange Protocol Version 2 (IKEv2) (obsoleted by RFC 7296)
See also[edit]
Dynamic Multipoint Virtual Private Network
Information security
NAT traversal
Opportunistic encryption
tcpcrypt
References[edit]
^ a b c Kent, S. ; Atkinson, R. (November 1998). IP Encapsulating Security Payload (ESP). IETF. doi:10. 17487/RFC2406. RFC 2406.
^ “Implementation of IPSec Protocol – IEEE Conference Publication”. 1109/ACCT. 2012. 64. S2CID 16526652.
^ Gilmore, John. “Network Encryption – history and patents”. Archived from the original on 2014-09-03. Retrieved 2014-02-18.
^ reserved, VTNV Solutions Limited www le-vpn com Sitemap © 2021 Le VPN All rights (August 17, 2018). “The History of VPN creation | Purpose of VPN”.
^ a b ”
^ ”
^ “IP Security Protocol (ipsec) -“.
^ “RFC4301: Security Architecture for the Internet Protocol”. Network Working Group of the IETF. December 2005. p. 4. The spelling “IPsec” is preferred and used throughout this and all related IPsec standards. All other capitalizations of IPsec [… ] are deprecated.
^ “NRL ITD Accomplishments – IPSec and IPv6” (PDF). US Naval Research Laboratories.
^ Thayer, R. ; Doraswamy, N. ; Glenn, R. IP Security Document Roadmap. 17487/RFC2411. RFC 2411.
^ Hoffman, P. (December 2005). Cryptographic Suites for IPsec. 17487/RFC4308. RFC 4308.
^ a b Kent, S. IP Authentication Header. 17487/RFC2402. RFC 2402.
^ a b c d e Kent, S. 17487/RFC4302. RFC 4302.
^ The Internet Key Exchange (IKE), RFC 2409, §1 Abstract
^ Harkins, D. ; Carrel, D. The Internet Key Exchange (IKE). 17487/RFC2409. RFC 2409.
^ Kaufman, C. (ed. IKE Version 2. 17487/RFC4306. RFC 4306.
^ Sakane, S. ; Kamada, K. ; Thomas, M. ; Vilhuber, J. Kerberized Internet Negotiation of Keys (KINK). 17487/RFC4430. RFC 4430.
^ a b Richardson, M. (February 2005). A Method for Storing IPsec Keying Material in DNS. 17487/RFC4025. RFC 4025.
^ Peter Willis (2001). Carrier-Scale IP Networks: Designing and Operating Internet Networks. IET. p. 270. ISBN 9780852969823.
^ a b “Protocol Numbers”. IANA. 2010-05-27. Archived from the original on 2010-05-29.
^ “SIPP Encapsulating Security Payload”. IETF SIPP Working Group. 1993. Archived from the original on 2016-09-09. Retrieved 2013-08-07.
^ “Draft SIPP Specification”. p. 21.
^ Bellovin, Steven M. (1996). “Problem Areas for the IP Security Protocols” (PostScript). Proceedings of the Sixth Usenix Unix Security Symposium. San Jose, CA. pp. 1–16. Retrieved 2007-07-09.
^ Paterson, Kenneth G. ; Yau, Arnold K. L. (2006-04-24). “Cryptography in theory and practice: The case of encryption in IPsec” (PDF). Eurocrypt 2006, Lecture Notes in Computer Science Vol. 4004. Berlin. pp. 12–29. Retrieved 2007-08-13.
^ Degabriele, Jean Paul; Paterson, Kenneth G. (2007-08-09). “Attacking the IPsec Standards in Encryption-only Configurations” (PDF). IEEE Symposium on Security and Privacy, IEEE Computer Society. Oakland, CA. pp. 335–349. Retrieved 2007-08-13.
^ Kent, S. 17487/RFC4303. RFC 4303.
^ Peter Willis (2001). p. 271. ISBN 9780852969823.
^ Peter Willis (2001). pp. 272–3. ISBN 9780852969823.
^ RFC 2406, §1, page 2
^ Thomas, M. (June 2001). Requirements for Kerberized Internet Negotiation of Keys. 17487/RFC3129. RFC 3129.
^ C. Cremers, Key Exchange in IPsec Revisited: Formal Analysis of IKEv1 and IKEv2, ESORICS 2011, published by Springer: ”
^ William, S., & Stallings, W. (2006). Cryptography and Network Security, 4/E. Pearson Education India. p. 492-493
^ Peter Willis (2001). p. 266. p. 267. ISBN 9780852969823.
^ RFC 2367, PF_KEYv2 Key Management API, Dan McDonald, Bao Phan, & Craig Metz (July 1998)
^ Hamad, Mohammad; Prevelakis, Vassilis (2015). Implementation and performance evaluation of embedded IPsec in microkernel OS. 2015 World Symposium on Computer Networks and Information Security (WSCNIS). IEEE. 1109/wscnis. 2015. 7368294. ISBN 9781479999064. S2CID 16935000.
^ RFC 6434, “IPv6 Node Requirements”, E. Jankiewicz, J. Loughney, T. Narten (December 2011)
^ “ipsecme charter”. Retrieved 2015-10-26.
^ “ipsecme status”. Retrieved 2015-10-26.
^ “Secret Documents Reveal N. S. A. Campaign Against Encryption”. New York Times.
^ John Gilmore. “Re: [Cryptography] Opening Discussion: Speculation on “BULLRUN””.
^ Theo de Raadt. “Allegations regarding OpenBSD IPSEC”.
^ Jason Wright. “Allegations regarding OpenBSD IPSEC”.
^ Theo de Raadt. “Update on the OpenBSD IPSEC backdoor allegation”.
^ David Adrian; Karthikeyan Bhargavan; Zakir Durumeric; Pierrick Gaudry; Matthew Green; J. Alex Halderman; Nadia Heninger; Drew Springall; Emmanuel Thomé; Luke Valenta; Benjamin VanderSloot; Eric Wustrow; Santiago Zanella-Béguelink; Paul Zimmermann. “Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice” (PDF).
^ Goodin, Dan (August 16, 2016). “Confirmed: hacking tool leak came from “omnipotent” NSA-tied group”. Ars Technica. Retrieved August 19, 2016.
^ Thomson, Iain (August 17, 2016). “Cisco confirms two of the Shadow Brokers’ ‘NSA’ vulns are real”. The Register. Retrieved September 16, 2016.
^ Pauli, Darren (August 24, 2016). “Equation Group exploit hits newer Cisco ASA, Juniper Netscreen”. Retrieved September 16, 2016.
^ Chirgwin, Richard (August 18, 2016). “Fortinet follows Cisco in confirming Shadow Broker vuln”. Retrieved September 16, 2016.
^
^ “key exchange – What are the problems of IKEv1 aggressive mode (compared to IKEv1 main mode or IKEv2)? “. Cryptography Stack Exchange.
^ “Don’t stop using IPsec just yet | Paul Wouters at more then 140 chars”.
External links[edit]
Computer Security at Curlie
All IETF active security WGs
IETF ipsecme WG (“IP Security Maintenance and Extensions” Working Group)
IETF
IPv6 Packet Security
Unlike IPv4, IPsec security is mandated in the IPv6 protocol specification,
allowing IPv6 packet authentication and/or payload encryption via the Extension
Headers. However, IPsec is not automatically implemented, it must be configured
and used with a security key exchange.
IPv6 Packet Structure
The IPv6 header is not variable, as in IPv4, but has a simple, efficient fixed
40-byte length. Minimum packet size is 1280 bytes, from 40 bytes of header plus
1240 bytes of payload.
Next Header Field
The Next Header field defines the type of header immediately following the
current one. It is usually the payload, but sometimes Extension Headers provide
valuable functions. Encryption capabilities are defined by the Authentication
and Encapsulated Security headers.
Extension Headers
Protocol numbers in required order of use
000 Hop-by-hop – must be examined by every node on path to destination
043 Routing header – list of nodes that should be visited on path
060 Destination options – processed by routers along path
044 Fragment header – packet was fragmented at source if too large for path
051 Authentication header – part of IPsec
050 Encapsulated security payload – IPsec
060 Destination options – processed at destination
Right: A simple IPv6 packet (top row) with a TCP
header and data payload. The second row shows the packet with an additional
Routing header, third row has Routing and Fragment headers.
IPv6 Packet Encryption
IPsec defines cryptography-based security for both IPv4 and IPv6 in RFC 4301.
IPsec support is an optional add-on in IPv4, but is a mandatory part of IPv6.
It provides two security headers which can be used separately or together:
Authentication Header (AH) and Encapsulating Security Payload (ESP), used in
conjunction with security key exchange.
Authentication Header
AH provides connectionless integrity, data-origin authentication and protection
against replay attacks. It authenticates with an Integrity Check Value (ICV)
calculated over the payload, the header, and unchanging fields of the IPv6
header and options. AH does not provide privacy and confidentiality of packet
contents. See RFC 2402.
Encapsulating Security Payload
ESP also provides connectionless integrity, data-origin authentication,
protection against replay attacks, limited traffic flow confidentiality, but
also provides privacy and confidentiality through encryption of the payload.
See RFC 2406.
IPsec Modes
IPSec operates in two different modes: Transport mode (host-to-host) and Tunnel
mode (gateway-to-gateway or gateway-to-host).
Transport mode: the IPv6 header of the original packet is used, followed
by the AH or ESP header, then the payload.
Tunnel mode: a new IPv6 header encapsulates the AH or ESP header and the
original IP header and payload.
Extension headers (Hop-by-Hop, Routing, Fragmentation) immediately follow their
IP headers, except for Destination Options, which can appear before or after AH
or ESP. (‘TCP’ below indicates any upper layer protocol. )
AH in Transport & Tunnel Modes
AH authenticates the packet and the outermost IPv6 addresses (except for
mutable fields), but does not encrypt payloads. AH cannot be used to traverse
NATs, as it calculates the integrity check value (ICV) over source and
destination addresses: NATs translate addresses, so would invalidate ICVs.
ESP in Transport & Tunnel Modes
ESP authentication does not include the outermost IPv6 headers, but in Tunnel
mode it protects the original headers. ESP is used to build virtual private
network tunnels between sites. It permits NAT traversal, as it does not use the
outermost address values in the ICV calculation. If AH and ESP are used
together, ESP is applied first, then AH authenticates the entire new packet.
The Security Association
Security Association is a record of the authentication algorithm, encryption
algorithm, keys, mode (transport or tunnel), sequence number, overflow flag,
expiry of the SA, and anti-replay window. The SA is held in a database at each
endpoint, indexed by outer destination address, IPsec protocol (AH or ESP), and
Security Parameter Index value.
Selection of SA can be manually (pre-shared keys) but preferably is automated
with Internet Key Exchange (IKE, IKEv2). IKE uses Diffie-Hellman techniques to
create a shared secret encryption key used to negotiate SA data. For key
exchange, IKE depends on a Public Key Infrastructure (PKI), which is not yet
widespread. The framework and syntax for key exchange is ISAKMP (Internet
Security Association and Key Management Protocol). See RFC 2408.
Frequently Asked Questions about ipsec ipv4 vs ipv6
Is IPsec an IPv4?
The IPsec is an open standard as a part of the IPv4 suite. IPsec uses the following protocols to perform various functions: Authentication Headers (AH) provides connectionless data integrity and data origin authentication for IP datagrams and provides protection against replay attacks.
Does IPsec work with IPv6?
Unlike IPv4, IPsec security is mandated in the IPv6 protocol specification, allowing IPv6 packet authentication and/or payload encryption via the Extension Headers. However, IPsec is not automatically implemented, it must be configured and used with a security key exchange.
Should I use IPv4 or IPv6 DNS?
Using both IPv4 and IPv6 for your nameservers is strongly recommended and is a task that is on the critical path to IPv6 deployment. Whether an enterprise is using their own on-premises DNS servers or a cloud-based DNS service, organizations should be making their DNS infrastructure dual-protocol.Aug 7, 2018