SOCKS Proxy Primer: What Is SOCKs5 and Why Should You …
co-authored by Darshan S. Mulimath, Megha B. Sasidhar, and Ashiq Khader
In computer networks, a proxy or proxy server is a computer that sits between you and the server. It acts as a gateway between a local network and a large-scale network, such as the internet.
A proxy server works by intercepting connections between sender and receiver. All incoming data enters through one port and is forwarded to the rest of the network via another port.
Aside from traffic forwarding, proxy servers provide security by hiding the actual IP address of a server. They also have caching mechanisms that store requested resources to improve performance. A proxy server can encrypt your data so it is unreadable in transit and block access to certain webpages based on IP address.
Now that we have a general sense of how a proxy works, let’s zoom in on a specific type of proxy — SOCKS — and, specifically, the SOCKs5 variant.
What Is a SOCKS Proxy?
SOCKS, which stands for Socket Secure, is a network protocol that facilitates communication with servers through a firewall by routing network traffic to the actual server on behalf of a client. SOCKS is designed to route any type of traffic generated by any protocol or program.
A SOCKS proxy server creates a Transmission Control Protocol (TCP) connection to another server behind the firewall on the client’s behalf, then exchanges network packets between the client and the actual server. The SOCKS proxy server doesn’t interpret the network traffic between client and server in any way; it is often used because clients are behind a firewall and are not permitted to establish TCP connections to outside servers unless they do it through the SOCKS proxy server. Therefore, a SOCKS proxy relays a user’s TCP and User Datagram Protocol (UDP) session over firewall.
SOCKS is a layer 5 protocol, and it doesn’t care about anything below that layer in the Open Systems Interconnection (OSI) model — meaning you can’t use it to tunnel protocols operating below layer 5. This includes things such as ping, Address Resolution Protocol (ARP), etc. From a security perspective, it won’t allow an attacker to perform scans using tools such as Nmap if they are scanning based on half-open connections because it works at layer 5.
Since SOCKS sits at layer 5, between SSL (layer 7) and TCP/UDP (layer 4), it can handle several request types, including HTTP, HTTPS, POP3, SMTP and FTP. As a result, SOCKS can be used for email, web browsing, peer-to-peer sharing, file transfers and more.
Other proxies built for specific protocols at layer 7, such as an HTTP proxy that is used to interpret and forward HTTP or HTTPS traffic between client and server, are often referred to as application proxies.
There are only two versions: SOCKS4 and SOCKs5. The main differences between SOCKs5 and SOCKS4 are:
SOCKS4 doesn’t support authentication, while SOCKs5 supports a variety of authentication methods; and
SOCKS4 doesn’t support UDP proxies, while SOCKs5 does.
A SOCKs5 proxy is more secure because it establishes a full TCP connection with authentication and uses the Secure Shell (SSH) encrypted tunneling method to relay the traffic.
Why You Should Adopt SOCKs5
Below are four key benefits to using a SOCKs5 proxy with SSH tunneling.
1. Access Back-End Services Behind a Firewall
Usually, a cluster is hosted in the cloud behind a firewall to minimize potential security vulnerabilities. There are two ways to access any backend services that are running inside a cluster, and each has its limitations:
Expose backend services to public (and accept the associated security risk); or
Whitelist the client or user’s IP to allow traffic to backend services (this is not the right solution for when a user’s IP changes, however).
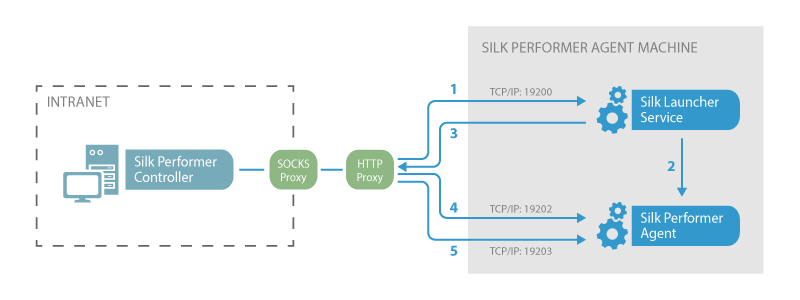
A SOCKs5 proxy with dynamic port forwarding using SSH can be an alternative to the two undesirable options above. An administrator or developer could access any backend services within a cluster that is hosted in the cloud behind a firewall for debugging, monitoring and administrating from a public network without exposing the backend service ports or whitelisting specific IPs.
Let’s look at a use case. For security reasons, the administration or monitoring application APIs or web user interface (UI) ports for monitoring Hadoop cluster are closed by default when hosted on the cloud. To access these APIs or web UIs, you can use SSH dynamic port forwarding to master or edge a node cluster, since the master node will have a public IP and run SSH services by default, which is exposed so the user can connect from outside.
For another example, say you’re working with a virtual private cloud (VPC). You can deploy a bastion host to securely access remote instances within a VPC by limiting their access to the outside world. You can access the bastion host from the outside world, and only port 22 (SSH) is opened. Using SSH dynamic port forwarding (SOCKs5 proxy), you can access the remote instances that are running in the VPC.
2. No Special Setup Required
SOCKs5 doesn’t require special setup, as long as you have SSH access to either the Edge node or gateway of a cluster. Therefore, users such as administrators and developers can access back-end resources behind the firewall using an SSH tunnel without requiring a virtual private network (VPN).
3. No Third-Party Public or Free Proxy Server in Your Deployments
Since a SOCKs5 proxy routes all kinds of TCP and UDP traffic to their respective service through SSH tunneling, no layer 7 application-related special proxies are required for each service to route application requests.
4. Fewer Errors, Better Performance
Unlike other application proxies, SOCKs5 does not rewrite data packets. It just relays the traffic between devices. Therefore, it is less prone to errors, and performance increases automatically.
How Does SOCKs5 Work in Practice?
Any CISO wouldn’t jump at the chance to embrace the benefits listed above. But what does a SOCKs5 proxy look like in the context of an enterprise security strategy? Where do security leaders begin when implementing SOCKs5 in their environment? Below are some key steps to help you get started.
Setting Up a SOCKs5 Proxy Connection
To SOCKSify an IT environment, the client application must have the capacity to support the SOCKs5 protocol. The syntax below is based on the SSH client on Linux; it shows how to create a SOCKs5 proxy server running on your local computer and then authenticate to the Edge node of a cluster or gateway hosted on cloud that routes traffic to the servers inside the cluster:
$ ssh -D 30001 [email protected] -C -f -N (password: xyz; or
$ ssh -i /path/to/private_key -D 30001 [email protected] -C -f -N
The above command starts the SOCKs5 server and binds to port 30001, then connects to Edge Node, Master Node or Gateway Node over the SSH tunnel hosted on the cloud.
The options used in the above command do the following:
D 30001 tells SSH to create a SOCKs5 server on port 30001 on the client computer.
C compresses data before sending.
N means “Do not execute a remote command. ” This is useful for simply forwarding ports (protocol version 2 only).
F requests SSH to go to the background just before command execution.
Accessing the Endpoints Using the SOCKs5 Protocol
Once a SOCKs5 proxy is created, configure your clients to access the internal services of the cluster. To keep it simple, we use a command line URL (cURL) that supports the SOCKs5 protocol. Other methods such as using a web browser require some additional setup and configurations.
The below cURL command shows how to access one of the HTTPS application endpoints listening on port 8000 behind a firewall using the SOCKs5 proxy over the SSH tunnel created above:
curl -x socks5hlocalhost:30001 -v -k -X GET EdgeNodeSSHserverIP:8000
The above cURL tool connects to port 30001 on localhost. Upon receiving a HTTP GET request on port 30001 from the cURL, the SSH client sends the same request via SSH tunnel to the SSH server.
The remote SSH server handles the request and passes the request to a back-end service listening at port 8000. The response is sent back to the client over the same SSH tunnel to the client’s SOCKs5 proxy. The proxy relays the response to the cURL, which displays the response.
Once you have created a SOCKs5 proxy using the SSH dynamic port forwarding method, you can also use the netcat utility to test the TCP connection. As shown below, a TCP connection test is made for back-end services listening at port 8443 with the SOCKs5 proxy:
ncat –proxy 127. 0. 1:30001 –proxy-type socks5 EdgeNodeSSHserverIP 8443 -nv
In Summary
A SOCKs5 proxy is a lightweight, general-purpose proxy that sits at layer 5 of the OSI model and uses a tunneling method. It supports various types of traffic generated by protocols, such as HTTP, SMTP and FTP. SOCKs5 is faster than a VPN and easy to use. Since the proxy uses a tunneling method, public cloud users can access resources behind the firewall using SOCKs5 over a secured tunnel such as SSH.

What is SOCKS5 Proxy and How to Set Up and Use It for Free
Updated on July 13, 2021: From now on, traffic filtering, malware protection, and suspicious DNS activity blocking are available as a part of the separate DNS Firewall CKS5 is a popular choice for netizens looking to protect their online activities, hide their real location, or bypass geo-blocking. KeepSolid offers SOCKS5 proxy for free, which you can learn how to get it in the following section of this article. But what is SOCKS5 proxy? How to setup and use free SOCKS5 proxy server? What’s the difference between SOCKS5 and VPN services? Let’s dig right into it! Get started with our reliable VPN solution and make your browsing more secure What is SOCKS5 Proxy
SOCKS (SOCKet Secure) is an internet protocol that forwards the user’s internet traffic through a proxy server. Any third-party observer will only be able to see the IP address of the SOCKS proxy server, not your real one.
This ensures that your online activities, sensitive information, physical location, and identity are protected from ISP, corporate, and even government surveillance (the extent of such proxy protection is limited, but we’ll discuss this later in the piece).
Difference between SOCKS4 and SOCKS5
SOCKS5 is the latest iteration of this free proxy protocol. It brings enough improvements to the table to make it unambiguously preferable than its predecessors in any situation. Here’s a quick summary of the differences between SOCKS4 and SOCKS5:
SOCKS5 is more universal. It supports a variety of authentication methods, while SOCKS4 doesn’t support authentication at all.
SOCKS5 proxy is more secure. It supports IPv6, TCP, and UDP proxies, while SOCKS4 only supports TCP.
How to Setup SOCKS5 Proxy
Then again, there is no reason not to try using SOCKS5 proxy and see how it fares. After all, you may not want to install a full-fledged cyber-security solution if all you need is a free SOCKS5 proxy to unblock Telegram.
Here’s how to setup SOCKS5 proxy and use SOCKS5 servers for free:
Consult the developer, documentation, or manuals of the app you want to use SOCKS5 proxy with to see if the application supports such an option.
Unless specified otherwise by the developer of the app in question, open its settings and find the section for SOCKS5 proxy configurations.
Enter the address and port of the server you want to connect to. SOCKS5 proxy servers currently available for free are:
USA NY (server address 142. 93. 68. 63, server port 2434)
Netherlands Amsterdam (server address 82. 196. 7. 200, server port 2434)
Singapore (server address 159. 89. 206. 161, server port 2434)
Enter login vpn and password unlimited
Benefits of SOCKS5 Proxy
As mentioned before, SOCKS5 protocol, if used properly, can be quite helpful in many occasions. The trick here is to know when it’s best to use proxy servers, and when you need other solutions. Let’s take a look at what free SOCKS5 proxy is best for.
Hide your location
As part of the modus operandi of the SOCKS5 protocol, all user traffic goes via a proxy server. This hides users’ actual location, instead causing the traffic to look like it originates from the location of the SOCKS5 proxy server.
Bypass geo-blocking and content censorship
Geographic content blocking occurs when a website, service, movie or show, video, etc. is banned in a particular region. But with SOCKS5 proxy you can virtually hop to a different location where the content is available (by selecting a respective server). An example of such use is that with proxy SOCKS5 you can access Telegram for free, even if it’s blocked in your country.
Improved security over other proxies
Proxies are universally considered quite unreliable and insecure. And even though SOCKS5 doesn’t eliminate all the perils associated with its counterparts, it’s still significantly more secure than them thanks to using internet protocols more secure than the common UDP.
Works at the application level
Since you set up SOCKS5 proxy server at the app level (we’ll explain how to do this later in the article), you can choose which programs on your device you want it to affect. This can be important if you only need free SOCKS5 proxy for a single specific app, or have complete control over which applications are affected.
SOCKS5 setup is only required once per app
After you’ve configured SOCKS5 proxy for an application, it will always automatically fire the proxy server connection upon launching the app (unless you wish to disable this option in the settings, obviously). Thus, you won’t have to remember to start it manually. Get top-notch protection on the web with VPN Unlimited SOCKS5 Proxy or VPN?
Now, let’s discuss shortcomings of SOCKS5 proxy and why an all-around privacy service like KeepSolid VPN Unlimited can be a more preferable choice in some cases.
Lack of security
The most prominent drawback of any proxy server, SOCKS5 proxy included, is the lack of data encryption. This means that whatever personal data or sensitive information you send off is totally unprotected from any malefactors. And you may be surprised to know how many cyber criminals are lurking about in the hunt for your passwords, credentials, online banking info, photos, private messages, search requests, etc.
Lack of independence
Another big issue of SOCKS5 proxy is its dependence on specific apps and their developers. You can only set up and use a SOCKS5 proxy server with an app if the application in question supports this option to begin with. Moreover, it means that if you wanted to connect multiple apps to the server, configuring them all will be quite a hassle. Compare it to VPN Unlimited, where you can protect the whole device (or, to be more precise, up to 5 devices with a single account) at once.
Lack of flexibility
Last but not the least, SOCKS5 proxy is less flexible than VPNs. Even the best free SOCKS5 proxies usually offer very few servers that are often cramped (causing lags) and inconveniently located. Compare this to VPN Unlimited servers: over 400 servers in 80+ locations all around the world, dedicated servers for torrenting and unblocking streaming services like Netflix, ability to buy Personal servers. Not to mention that you can switch servers on the fly, whereas with SOCKS5 you’d have to manually enter the new server’s settings every time.
SOCKS5 proxy vs. VPN Unlimited comparison
All in all, it’s highly recommended you use VPN Unlimited over SOCKS5 proxy if you are concerned about your online security and the integrity of your personal data, or need anything more than hiding your IP or bypassing basic geo-blocking. If you’re still not sure, you can try VPN Unlimited for free to see if it suits your needs. Get started with VPN Unlimited right now Grab your 7-day free trial and 30-day money-back guarantee to check out KeepSolid VPN Unlimited features!
Differences between http proxy vs socks proxy – Limeproxies
The world of proxies can be confusing and technical for you if you are new to it. When making use of a private proxy like limeproxies, you will encounter jargon and technicalities that can be overwhelming. There are different types of proxies and a lot of terminologies, but learning about the differences allows you to have a better understanding of how everything works. In this article, we will dwell on differences between HTTP proxy vs SOCKS proxy.
Once you understand the workings and technicalities of using proxies, you will have access to web content that was previously blocked to your access due to geographical restrictions. Having access to websites that lockout offshore access will no longer be a problem for you. Good knowledge of proxies also help you easily swap between different types of proxy and port numbers so that you can find out which option works best for you in each usage Quick LinksJump straight to the section of the post you want to read:SOCKS PROXIESHTTP PROXYWHAT DO YOU KNOW ABOUT PORTS? DIFFERENCES BETWEEN PROXIES: HTTP PROXY VS SOCKS PROXYA BREAKDOWN OF HTTP PROXY VS SOCKS PROXYSOCKS PROXIES
The web is made up of protocols that make it easy to communicate from both ends (user and the internet). What you call the internet is made up of several protocols that come into play.
SOCKS is an acronym that stands for secure sockets. It is a type of proxy that is used for general needs.
It is a protocol that creates a TCP (Transmission Control Protocol) connection with a different server. Once the connection has been made between the client and the server, the exchange of data can begin. SOCKS proxy can be used to gain access to sites that have a firewall, preventing regular internet access. It gives access to a TCP that has been otherwise blocked.
The best feature of using SOCKS is that you can have a connection with TCP without having to reduce the integrity of your firewall. You will remain protected by your firewall even if you bypass it for a few moments of browsing anonymously. Another big side to using SOCKS proxy is that you will not make use of penetrative data. Your SOCKS connection can be used with any type of proxy with any type of connection. It doesn’t matter whether your network is leveraging any type of network protocol.
SOCKS 4 provides you with good enough security for the average internet user. It is the most commonly available proxy of this type and acts as the default connection. If you are not just an average internet user and need more security and safety online, SOCKS 5 is the connection you should make use of. It gives you improved authentication options that allow you to add more layers of security to your proxy. This keeps you anonymous and heavily secures your data.
HTTP PROXY
HTTP is another protocol that is very popular. It functions on a higher level than SOCKS and so is able to better understand the traffic coming over a TCP connection. This is one feature a SOCKS connection cannot properly provide.
With the use of HTTP proxy, requests can be received directly from applications that also use HTTP as their protocol. Being limited in that way may seem like a disadvantage especially if you need security across all your online activity, but the truth is HTTP proxies interface with specific connections in ways that SOCKS never could.
Although HTTP proxies do have some limitations that SOCKS do not have, their ability to properly understand data is an endearing factor. HTTP is more attractive if you need the proxy to scrape a site or run a bot.
For instance, running a scraping software over an HTTP proxy will help you extract what is needed from the website, leaving behind what is not needed. The result is s clean data that is easier to work with. It helps you utilize your time properly as you do not have to waste any second going through useless data to get out the necessary information.
HTTPS PROXY
The HTTPS proxy allows you to have a more secure connection. For the safety of the data you transmit, HTTPS proxies give you the feature of having an unreadable data if intercepted. When connecting to an intranet or your bank from abroad, your best choice would be to do so with an HTTPS proxy.
WHAT DO YOU KNOW ABOUT PORTS? It is good that you pay attention to the port number your proxy uses. A particular proxy may require communication over a certain port number for it to function properly and create a connection.
When you assign a proxy to a specific port number, it communicates through that port. It has access to data that is sent or received through that port number. SOCKS protocols support most proxy ports on a computer, but using HTTPS often requires that you make use of port number 443, and HTTP is often set at 80.
Even though HTTP and HTTPS protocols will provide you with greater access to web applications and can assist software in interpreting data, a SOCKS proxy is useful as a simpler option and works on almost any port number. This makes it easier to set up when there are port restrictions at the network level. Both SOCKS and HTTPS proxies have their place and are useful respectively.
DIFFERENCES BETWEEN PROXIES: HTTP PROXY VS SOCKS PROXYA SOCKS proxy is a general-purpose proxy. It establishes a TCP connection to another server on behalf of a client and routes all the traffic between the client and the server back and forth. SOCKS works on any kind of network protocol on any port. SOCKS 5 gives additional security.
SOCKS doesn’t interpret network traffic but is used to access connections outside a firewall that limits the client’s access. Most web browsers can be configured to exchange data with a web server through a SOCKS server. To make such connections, the client must first be SOCKS enabled so as to be able to make a connection to the SOCKS server and tell it the host it wants to connect to.
An HTTP proxy is similar to a SOCKS proxy because it can also be used to make TCP connections when the clients are within a firewall. Unlike SOCKS proxies, however, HTTP proxies understand and interpret the network traffic between the client and server (HTTP protocol). HTTP proxy can be used to handle only HTTP traffic and in a smart way. It recognizes repeated requests and caches the replies so as to improve performance. Many ISPs make use of HTTP proxies not minding the browser configuration by simply routing all traffic on port 80 through the proxy server.
A BREAKDOWN OF HTTP PROXY VS SOCKS PROXYWhat is of the utmost importance today in the world of the internet is privacy and anonymity as you use the web. There are major breaches each day that exposes personal details to the wrong individuals. Facebook, Google, Twitter, and other credit bureaus among others have all had their fair share of breaches. Besides these, it is common knowledge that some government and private agencies spy on people’s internet use. To avoid having your details and personal information getting into the wrong hands, the use of a proxy is recommended.
There are a lot of options with which you can stay anonymous while online, but both SOCKS and HTTP proxies offer you great flexibility and reliability than most others. If you are faced with the dilemma of making a choice between SOCKS vs HTTP proxy, having more information on both will help you.
HTTP PROXY VS SOCKS PROXY; WHICH IS RIGHT FOR YOU?
There is no competition between HTTP vs SOCKS as the right proxy for you depends largely on what it is you intend to do online.
HTTP/HTTPS proxies offer you a great deal of encryption so you stay safe. You will be able to have 100% protection of the data you send as it goes through the server. Furthermore, you can stay anonymous and hide your online activity from your ISP. So you do not have to worry about your information getting into the wrong hands, it allows you to avoid throttling, and you are protected when downloading large files or using torrents.
A good number of HTTP/HTTPS solutions are available for free. These guides take you step by step to help you up and running and make use of their free proxy options. You already know that there is danger involved with using free proxies because you do not know who is running the service. You could be exposed to viruses or malware, and some servers maintain a user log that keeps a record of your usage.
The use of HTTP will only work if your data is HTTP as well. So you will have a bit of a problem here if you want to transfer information over UDP, POP3, or other non HTTP networks.
SOCKS allows you to connect easily and fast with any network as it supports both TCP and UDP transfer protocols. It also ensures that your data packet headers are not rewritten. So you have no worries about misrouting or mislabeled data packets, improving your proxy stability and avoiding errors that slow down the connection.
SOCKS 5 makes use of no logs whatsoever, so you are completely anonymous and your usage is not monitored. This means that they can be no accidental discovery of whatever you do because there is no record.
The argument of the superior when it comes to SOCKS vs HTTP proxies is dependent on what you need a proxy for. These two are good and offer you good layers of security and anonymity which is basically what you need a proxy for. But if you are considering other uses online, then it is best to make use of the one that best suits your purpose. By now you should have good knowledge of the strengths and weaknesses of each protocol. Make use of the knowledge to your advantage to get the best out of your the authorRachael ChapmanA Complete Gamer and a Tech Geek. Brings out all her thoughts and Love in Writing Techie to get started? Try it free for 3 days
**SOCKS PROXY**
**HTTP PROXY**
SOCKS proxy works on any network protocol and on any port
Chances of your data being viewed is low since SOCKS doesn’t read data
There is a chance that your data can be viewed since your activity is stored in a log
It is a general server and the speed is fast
It could be fast or slow, depending on your choice of either a private or public proxy
Connects to fewer tools than HTTP proxy
Connects easily with a wide range of tools
It is considered a lower level proxy because of its use as a general purpose proxy
Vital for information retrieval from the web
Frequently Asked Questions about socks proxy port
What are SOCKS in scamming?
SOCKS, which stands for Socket Secure, is a network protocol that facilitates communication with servers through a firewall by routing network traffic to the actual server on behalf of a client. SOCKS is designed to route any type of traffic generated by any protocol or program.Sep 27, 2019
Where can I find SOCKS5 proxy?
SOCKS5 proxy servers currently available for free are:USA NY (server address 142.93. 68.63, server port 2434)Netherlands Amsterdam (server address 82.196. 7.200, server port 2434)Singapore (server address 159.89. 206.161, server port 2434)Feb 16, 2020
What is the difference between sock and proxy?
A SOCKS proxy is a general-purpose proxy. It establishes a TCP connection to another server on behalf of a client and routes all the traffic between the client and the server back and forth. … SOCKS doesn’t interpret network traffic but is used to access connections outside a firewall that limits the client’s access.Jan 20, 2020